Increased data breaches have intensified the need for more cloud security software. An example of such technology is cloud security posture management (CSPM). The CSPM manages staff configuration issues, provides cloud environment assessment and offers alerts to staff on configuration issues as well as compliance risks that emanate from human error that may compromise security. An example of issues that can occur due to human error is in the case of Capital One back in 2019. In this case, an ex-Amazon Web Services (AWS) employee exploited a misconfigured Web Application Firewall of Capital One, a financial service provider gaining access to crucial data.
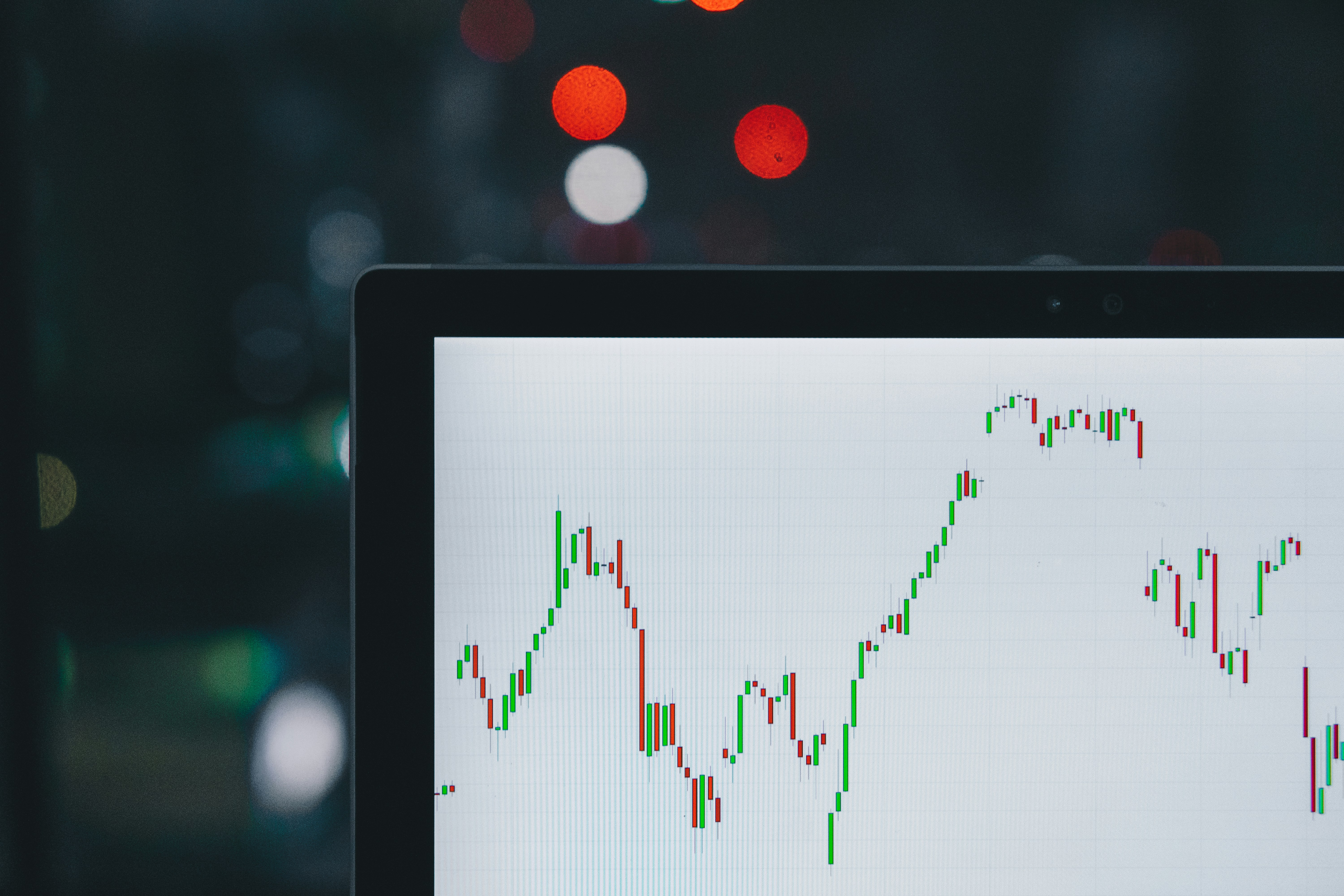
As evidenced by the above scenario, misconfiguration is a big mistake in the cloud environment. Although professionals try their best to configure cloud applications, human error is inevitable in most instances. Small as they may seem, such mistakes may leave an organization susceptible to attacks through its networks and hardware. According to Neil MacDonald, some of the mistakes that occur that allow hackers to gain access to critical resources in a network are permissions and access pints. These areas leave the cloud susceptible. Accordingly, Gartner notes that as opposed to the thinking that the mistakes are from the cloud service provider, the truth is that 90 percent of the mistakes originate from the customers’ end. Most of the problems here are due to poor configuration of permissions and privileges. The speed that deployment is done is often to be blamed for this since management often asks developers to meet unrealistic deadlines.
The increase in the adoption of the cloud has seen the rising importance of operating the right cloud configurations. According to MacDonald, companies need to tackle this challenge by investing in CSPM suites that are an extension of Cloud Access Security Broker Software (CASB). These two allows CIOs to understand the people whom thousands of accounts are provisioned for, the permissions that each of these people have and the type of data that these individuals can share and with whom they can share.
Since many customers and their data is stored in the cloud, many doors or vulnerable areas are opened. These areas can allow perpetrators to get into the company’s systems and cause damage that will take long to fix. To be sure of the potential points of weakness is another challenge. It even becomes more complicated in the modern era characterized by different API’s that have different privileges and opens different communication ports. As such, it is prudent that these API’s and ports are checked accordingly before granting them access.
While picking a cloud service provider may be important, having the right people in the organization to manage it is even more critical as many mistakes originate from the organization itself. As such, CIOs must take charge and ensure that all security measures are taken care of, and configurations are conducted as it should be to avoid unnecessary losses.